The e-commerce industry’s drive to innovate has enabled rapid growth, faster customer experiences, and greater operational agility, but it has also introduced technical complexity that is difficult to secure at scale. Outdated libraries, unpatched code, and loosely governed third-party integrations are often embedded deep within production systems, creating vulnerabilities that are easy to miss and challenging to remediate.
At the same time, e-commerce platforms process large volumes of sensitive customer data across distributed, fast-moving architectures. From payment systems to marketing analytics, every integration expands the potential attack surface. Without a scalable, risk-based approach to security, critical issues often remain hidden until they are exploited.
What are the issues?
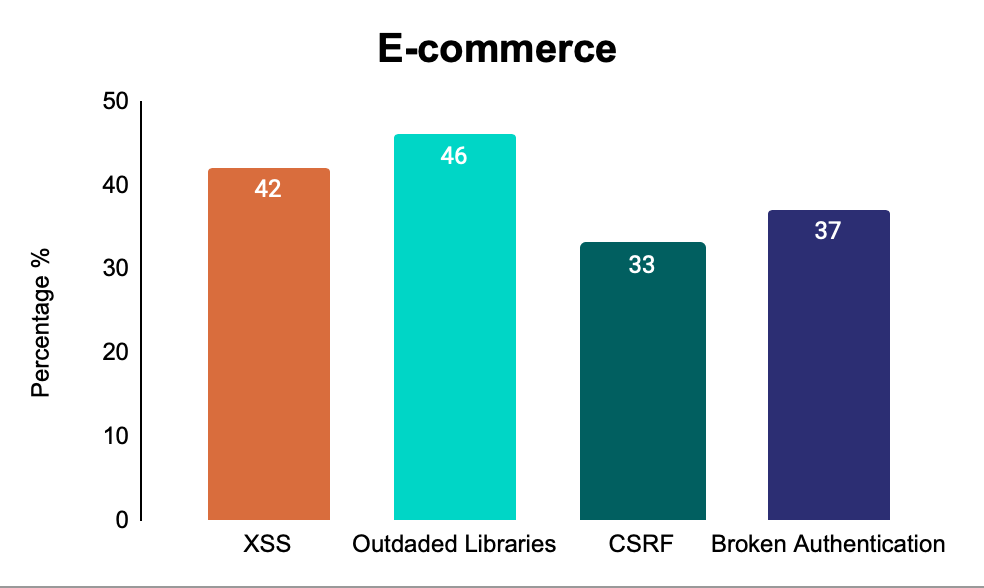
According to insights from our research team, the following vulnerabilities are most commonly identified in the e-commerce industry:
- 46% of security issues stem from outdated libraries, these dependencies are often deeply embedded and rarely prioritised, despite being well-known entry points for attackers.
- 43% are related to Cross-Site Scripting (XSS) frequently leveraged in credential theft, session hijacking, and browser-based attacks.
- 37% involve broken authentication, leaving account takeovers and privilege escalation on the table.
- 33% stem from Cross-Site Request Forgery (CSRF), a vulnerability type that should be obsolete, yet is still frequently found in production.
Even more concerning, critical vulnerabilities remain open for an average of 83 days, while high-severity issues take over 110 days to remediate. In the e-commerce sector, where speed and customer trust are everything, that level of exposure is unsustainable.
The Strain on Security and Development Teams:
Security leaders in e-commerce face a familiar challenge: managing a growing backlog of vulnerabilities with limited time, tools, and headcount. In many organisations, responsibility for remediation is shared and often blurred between security and development teams, each already stretched thin by competing demands.
These teams are expected to respond to threats, maintain compliance, deliver new features, and ensure platform stability — all at once. In this environment, vulnerability management often becomes a case of “known, but not fixed.”
Without clear ownership and efficient processes, issues are deferred, reliance on scheduled scans increases, and opportunities to catch and fix vulnerabilities earlier in the development cycle are missed. Over time, this pushes teams further into reactive firefighting, making it harder to reduce risk in a meaningful way.
Why CISOs Must Prioritise Risk Reduction Today:
This is not a visibility issue. Most CISOs are fully aware of where the vulnerabilities are. The problem is that traditional, tool-centric approaches: scan, ticket, triage, repeat, which no longer work at the speed or scale of modern e-commerce operations.
In many organisations, the website is owned by commercial or marketing teams, whose priorities lie in design, speed, and customer experience. Security, often managed by a separate IT or SecOps function, operates under entirely different KPIs, with risk reduction and compliance at the core. These conflicting objectives can slow down remediation efforts, create tension across teams, and lead to critical issues remaining unresolved for far too long.
This is not a tooling problem, it is an operational one. And without structural change, the gap between exposure and action will only widen.
CISOs must take ownership of three critical priorities now:
- Close the Detection-to-Fix Gap
Knowing about a vulnerability is not enough. It must be understood in context, prioritised by impact, and resolved efficiently. Hackurity’s platform delivers validated findings enriched with exploitation context, helping teams to address high-risk issues first, without drowning in alert noise.
- Reduce Friction for Overloaded Teams
Security and IT teams are under constant pressure. Hackurity helps alleviate this by integrating directly into existing developer and SecOps workflows, eliminating manual overhead and providing actionable insights instead of raw data. The result? Fewer tickets, faster fixes, and less back-and-forth.
- Modernise Vulnerability Management Workflows
Legacy vulnerability management tooling is ill-equipped for the scale and speed of e-commerce. Hackurity combines intelligent automation with expert validation to deliver continuous, real-world testing that keeps pace with release cycles and architectural change.
Hackurity: Elevating Cybersecurity with Managed Autonomous Pentesting:
The challenge isn’t just identifying vulnerabilities, it’s keeping pace with them as attackers evolve their tactics daily. That’s where Hackurity’s Managed Autonomous Pentesting (MAP) comes in. Instead of relying on periodic, manual tests that leave long blind spots, MAP continuously simulates real-world attacks across your E-commerce environment, including web apps, APIs, and infrastructure. The result is clear visibility into exploitable weaknesses, prioritised by business impact, with expert guidance to remediate them before adversaries can strike.
Every promo, plugin, and payment flow widens your attack surface. MAP keeps testing it, so you catch what matters before it costs you revenue or trust. Want a tailored view of your exposure? Request a MAP demo.
About Hackurity
Hackurity is the always-on, autonomous cybersecurity platform that reduces risk and complexity by protecting organisations continuously, from vulnerability discovery and exploitation to full remediation. Combining real-time automated penetration testing with expert human insight, we detect, test, and neutralise threats before they become breaches. By removing noise and turning security into an operational strength, Hackurity frees businesses to scale with confidence, knowing their risk is minimised and their cybersecurity is handled, simply and proactively.